Is Your Contact Center Secure? Here's How
Your call center security depends on a multi-layered strategy, not a single tool. This is crucial in a world where data privacy is a major issue for customers.
- 86% of the US population views data privacy as a growing concern.
- 40% of US consumers do not trust companies to use their data ethically.
True call center security combines robust technology, strict operational processes, and continuous employee training. Following these pillars helps you protect sensitive customer information. It also allows you to meet the standards of a secure customer contact center. This approach builds the trust that customers demand. Platforms like Sobot provide a secure technology foundation for this essential strategy.
Build a Secure Technology Foundation for Call Center Security
Your technology is the first line of defense against threats like hacking, ransomware, and insider data theft. A strong technical framework is not optional; it is the bedrock of your entire call center security strategy. You can build this foundation by focusing on four key areas.
Implement Strong Access Controls
You must control who can access customer data. Implementing a Role-Based Access Control (RBAC) system ensures employees only have access to the information necessary for their jobs. This principle of "least privilege" minimizes risk. You can start by:
- Defining specific roles within your team.
- Assigning access permissions based on each role's duties.
- Regularly reviewing and updating these roles.
To further secure logins, you should enforce multi-factor authentication (MFA). This requires users to provide two or more verification factors to access an account, making it much harder for unauthorized users to gain entry to systems containing sensitive information.
Encrypt All Sensitive Data
Encryption transforms readable data into an unreadable code. This is one of the most effective data security measures you can take. You must protect data in two states:
- Data in transit: Information moving across your network or the internet.
- Data at rest: Information stored on servers, hard drives, or in the cloud.
For robust protection, use industry-standard encryption algorithms like AES-256. This standard is trusted by governments worldwide and makes data virtually impenetrable to hackers, even if they breach your network.
End-to-end encryption ensures that communications, like calls or chats, are secure from the sender to the recipient, with no one in between able to decipher them.
Utilize Secure Network Configurations
Your network architecture must be designed for security. Use firewalls to monitor and control incoming and outgoing network traffic, acting as a barrier against cyber threats. For remote agents, a Virtual Private Network (VPN) creates a secure, encrypted tunnel to your central systems.
Beyond prevention, you need active threat monitoring. Network segmentation divides your network into smaller, isolated sections. If one segment is compromised, the breach is contained and cannot spread. Continuous threat monitoring helps you detect and respond to suspicious activity in real-time, which is vital for modern call center security.
Deploy a Unified, Secure Platform
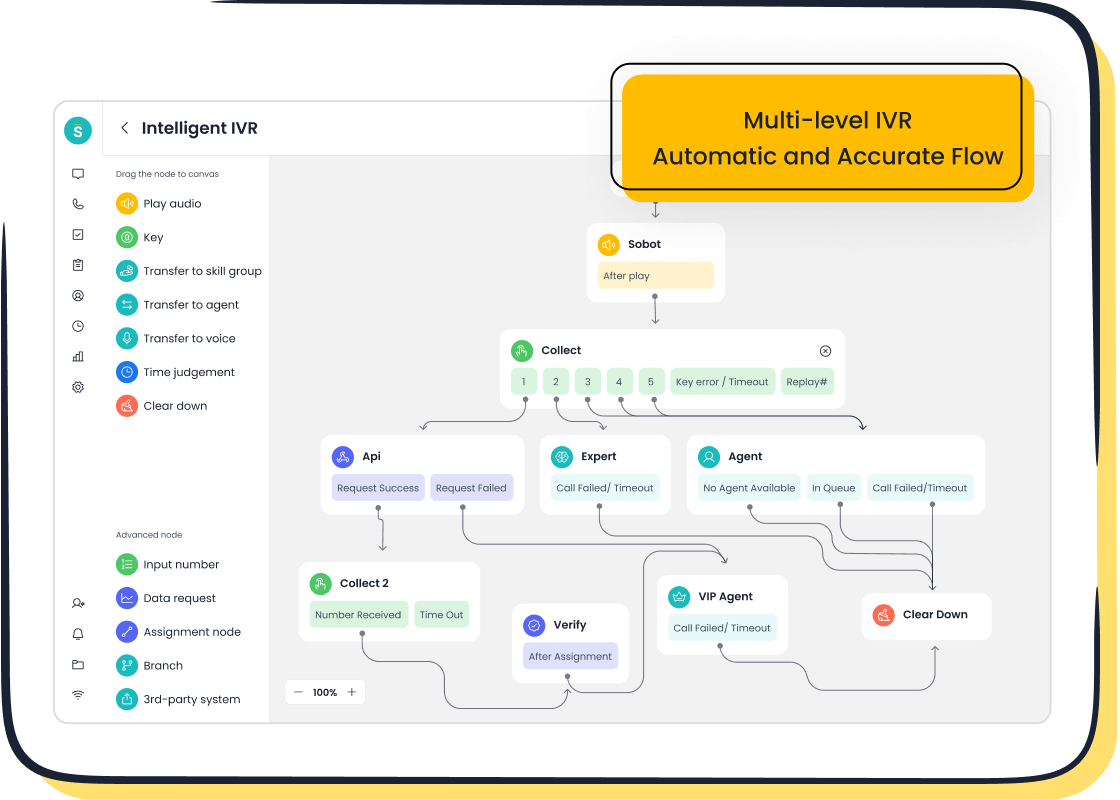
Using separate, disconnected systems creates data silos that are difficult to secure and monitor. A unified platform consolidates your tools into a single, secure workspace, reducing vulnerabilities. Solutions like Sobot's Voice/Call Center provide this all-in-one environment.
Platforms like Sobot enhance call center security by design. They offer features such as encrypted data transfer for all communications and guarantee reliability with a 99.99% system uptime SLA. This level of availability minimizes disruptions that attackers could exploit. Integrating tools like a ticketing system and live chat into one platform centralizes customer data, making it easier to manage, monitor, and protect with consistent encryption and access policies.
Meet the Standards of a Secure Customer Contact Center
Technology alone is not enough. Your operational processes must support your security goals to meet the high standards of a secure customer contact center. This involves creating clear rules for handling data from its creation to its disposal. Building these processes establishes a framework that protects your customers and your business.
Establish Protocols for Protecting Customer Data
You need clear, documented protocols for protecting customer data. Start by defining how agents verify a customer's identity using methods like one-time passwords (OTPs) sent via SMS. Your team must know exactly what to do and what to avoid when handling sensitive information. Following these guidelines is essential for maintaining the standards of a secure customer contact center.
| Do ✅ | Don't ❌ |
|---|---|
| Encrypt all devices and data. | Send sensitive information via unsecure email. |
| Use strong, unique passwords. | Share login credentials with anyone. |
| Lock your computer when away. | Leave customer data visible on your screen. |
Maintain Strict Compliance Adherence
Your contact center must follow key data privacy regulations. These rules set the legal standards of a secure customer contact center. Important regulations include:
- PCI DSS for protecting credit card information.
- HIPAA for securing patient health data.
- GDPR for handling the personal data of EU citizens.
Managing compliance across email, chat, and phone calls can be complex. An omnichannel solution like Sobot's simplifies this. It centralizes customer interactions from all channels into one platform. This makes it easier to monitor activities, apply consistent security rules, and prove compliance, helping you meet the standards of a secure customer contact center.
Enforce a Clear Security Policy
You must create and enforce strong security policies that every employee understands. This policy should define roles and responsibilities, outline data handling procedures, and establish an incident response plan. It also needs to address modern challenges like Bring-Your-Own-Device (BYOD) rules, specifying how personal devices can connect to your network securely. A clear policy removes guesswork and builds a culture of security.
Implement Secure Data Disposal
When you no longer need customer data, you must destroy it securely. Simply deleting files is not enough, as data can often be recovered. Improper disposal can lead to massive fines and reputational damage. Implement a formal data disposal process that includes methods like physical shredding of hard drives. Using a certified service ensures the data is gone forever, which is a critical final step in upholding the standards of a secure customer contact center.
Empower People for Better Call Center Data Security

Your technology and processes are strong, but your team is the final, critical layer of defense. Human error can lead to a serious data breach, so empowering your people is essential for true call center data security. You must equip them with the knowledge and mindset to recognize and stop data security threats.
Train Agents to Protect Customer Data
Your agents are on the front lines. Regular training is crucial to help them protect customer data effectively. Your training program should teach agents how to:
- Verify a customer's identity before sharing any information.
- Recognize common data security threats, like suspicious requests.
- Understand their role in preventing a data breach.
Use interactive methods like gamification to make learning engaging. Adding points, badges, and leaderboards to training can boost employee engagement and knowledge retention, making complex security concepts easier to remember.
Conduct Routine Security Audits
You need to regularly check your security measures to ensure they are working. Routine security audits help you find and fix vulnerabilities before they cause a data breach. During an audit, you should assess key areas like:
- Access Controls: Check who has access to what information.
- Network Security: Review your firewalls and VPN configurations.
- Data Encryption: Confirm that data is encrypted both at rest and in transit.
These regular checks help you maintain compliance and protect against evolving data security threats.
Identify Phishing and Social Engineering
Attackers often use phishing and social engineering to trick agents into giving up sensitive information. A common tactic involves a caller pretending to be from technical support to gain credentials. Train your team to spot these red flags. Use realistic simulations, like fake phishing emails or vishing calls, to give agents hands-on practice. This prepares them to handle real-world attacks and prevent a costly data breach.
Foster a Security-First Culture
Ultimately, you want to build a culture where security is everyone's responsibility. This starts with leadership modeling good security habits. When you combine a well-trained team with powerful technology, you create a resilient defense. For example, Samsung implemented Sobot's all-in-one solution to unify its operations. This move, combined with proper agent processes, boosted agent efficiency by 30% and achieved a 97% customer satisfaction rate. This shows how the right tools empower a security-conscious team to not only protect customer data but also deliver exceptional service. A strong culture is your best defense against a data breach and the foundation of long-term call center data security.
Securing your contact center is an ongoing commitment, not a one-time project. Your defense against evolving threats relies on integrating secure technology like Sobot, strict operational processes, and a well-trained team. This multi-layered approach creates a resilient framework for call center security. By embracing these pillars, you can protect customer data and confidently answer "yes" when asked about your call center security.
FAQ
What is the first step to improve my call center security?
You should start by adopting a multi-layered strategy. This approach combines secure technology, strict operational processes, and continuous employee training. A single solution is not enough to protect your contact center and customer data effectively.
How does a unified platform enhance security?
A unified platform like Sobot's Voice/Call Center centralizes your tools into one secure workspace. This reduces vulnerabilities from disconnected systems. It simplifies monitoring, enforces consistent security policies, and ensures features like encrypted data transfer protect all interactions.
Why is employee training so important for data security?
Your employees are a critical line of defense. Proper training empowers them to recognize and prevent threats like phishing and social engineering. A security-first culture, built through training, turns your team into an active part of your security framework.
How can I ensure my contact center meets compliance standards?
You must adhere to regulations like PCI DSS, HIPAA, and GDPR.
An omnichannel solution helps centralize customer data from all channels. This makes it easier for you to apply security rules, monitor interactions, and generate reports to prove compliance across your entire operation.
See Also
Evaluating Leading Contact Center Solutions: A Comprehensive Review for 2024
Exploring Premier Cloud Contact Center Services: In-Depth Reviews for 2024
A 10-Step Guide to Implementing Effective Omnichannel Contact Center Solutions
Discovering the Foremost Cloud Contact Centers: An Exclusive Look for 2025
Essential Principles: A Comprehensive Guide to Quality Management Systems for Call Centers