Secure Your Service Tool 10 Key Features for 2026
Customer interactions are data-rich, making tool security paramount. Consumers demand strong data protection; a recent survey showed 87% would not do business with a company if they had concerns about its security practices. This checklist defines the essential security requirements for a customer service tool. These 10 security features are critical for data protection, regulatory compliance, and business reputation. Platforms like Sobot are built around these advanced security features, ensuring that all security requirements for customer service tool are met.
- End-to-End Encryption (E2EE) Features
- AI-Powered Threat Detection
- Granular Role-Based Access Control (RBAC)
- Advanced Multi-Factor Authentication (MFA)
- Security Information and Event Management (SIEM)
- Automated Data Redaction and Masking
- Robust API and Integration Security
- Geofencing and IP Whitelisting
- Global Compliance Features
- Secure Software Development Lifecycle (SSDLC)
1. End-to-End Encryption (E2EE) Features
Essential Data Protection
End-to-End Encryption (E2EE) is the cornerstone of modern data protection. This method scrambles data at its origin and only unscrambles it at its final destination. No one in between, not even the service provider, can read the information. This level of security is non-negotiable for customer service tools that handle a constant flow of Personally Identifiable Information (PII).
Recent data breaches highlight the exact types of sensitive information at risk. Attackers frequently target customer service platforms to steal valuable data for financial fraud or identity theft.
| Incident | Data Exposed |
|---|---|
| Air France and KLM Breach | Passenger names, email addresses, phone numbers, loyalty program numbers |
| TransUnion Breach | Names, addresses, phone numbers, Social Security numbers, support tickets |
E2EE directly protects this data in transit and at rest. It ensures that even if a system is compromised, the underlying customer information remains encrypted and useless to attackers.
Key 2026 Capabilities
Looking toward 2026, the standard for encryption is evolving to counter future threats, particularly from quantum computing. Quantum computers threaten to break today's encryption standards. Malicious actors are already using a "Harvest Now, Decrypt Later" strategy, collecting encrypted data today to break it with future technology.
Organizations are urged to explore and adopt quantum-resistant key protocols now to future-proof their cybersecurity strategies against emerging quantum threats.
Leading service tool providers must therefore implement Post-Quantum Cryptography (PQC). The U.S. National Institute of Standards and Technology (NIST) has already released its first finalized PQC standards, setting a new benchmark for the industry. Tech leaders like Microsoft are actively integrating these new algorithms across their core services. A forward-thinking customer service platform for 2026 will feature these next-generation encryption protocols, demonstrating a proactive commitment to long-term data security.
2. AI-Powered Threat Detection
Proactive Defense Mechanisms
Traditional security tools rely on fixed rules. They can only stop known threats, leaving businesses vulnerable to new attack methods. AI-powered threat detection moves beyond this reactive model. It uses machine learning for proactive monitoring, identifying anomalies and potential threats in real time. This intelligence allows security automation tools to neutralize a threat before it causes a significant incident.
Instead of overwhelming teams with false alarms, AI provides a focused response. It learns what normal activity looks like and flags only true deviations, dramatically improving detection accuracy. This shift from high-volume alerts to actionable intelligence is critical for an effective security posture. The difference in performance is stark.
| Key Metric | Rule-Based Systems | AI-Driven Solutions |
|---|---|---|
| Detection Accuracy | Moderate (often >60% false positives) | High (reduces false positives by 90%) |
| Alert Volume | Overwhelming for security teams | Optimized based on risk scoring |
| Adaptability | Rigid, requires manual updates | Continuously adapts to new threats |
This advanced approach to threat detection and response ensures that security teams can focus their efforts on genuine threats, strengthening the overall defense.
Advanced Behavioral Analytics
Advanced behavioral analytics is the engine behind modern AI security. The system establishes a baseline of normal user and system behavior within the customer service tool. It analyzes patterns like login times, data access frequency, and communication styles. Any deviation from this baseline triggers an immediate response, enabling rapid threat detection. This capability is essential for effective threat hunting and incident prevention.
Platforms like Sobot's AI Solution for retail and e-commerce use this principle effectively. The solution incorporates behavioral analytics to protect customer data during online interactions, aligning with modern security needs for a smarter response. This real-time monitoring and intelligence gathering turns raw data into actionable intelligence. It allows incident response tools to act on a potential threat with precision.
Modern tools leverage AI not just for detection, but for automated response. This real-time response capability contains threats instantly, minimizing the potential for data loss and operational disruption.
By integrating threat intelligence integration, these systems enhance their detection capabilities even further. This continuous loop of detection, analysis, and response makes AI-powered security automation tools a non-negotiable feature for 2026, providing superior detection accuracy and a more resilient defense against evolving threats.
3. Granular Role-Based Access Control (RBAC)
The Principle of Least Privilege
Granular Role-Based Access Control (RBAC) is a fundamental method for managing user permissions. It operates on the principle of least privilege. This principle dictates that users should only have access to the information and tools necessary to perform their jobs. In a customer service environment, this means a support agent for one product line cannot view the customer data of another. A manager might have permission to view team performance reports but not to export the entire customer database.
This approach significantly reduces the risk of data breaches. It limits the potential damage from a compromised account. It also prevents accidental data exposure by well-meaning employees. Implementing strict RBAC is a critical layer of internal security. It ensures that sensitive customer information remains confined to authorized personnel, protecting both the customer and the business from unnecessary risk.
Dynamic and Context-Aware Controls
By 2026, static roles are no longer sufficient. Customer service platforms must offer dynamic, context-aware access controls. These systems adapt permissions in real time based on the user's situation. This is especially vital for managing a modern hybrid workforce. A robust system automatically adjusts access based on several factors.
Note: Dynamic controls are essential for securing a workforce that is no longer tied to a single office. They provide flexibility without compromising on protection.
These controls evaluate access requests based on the current context, enhancing security without disrupting workflow. Key capabilities include:
- Securing Remote Work: The system can evaluate an employee's device trust level and geographic location. It can deny access if a login attempt comes from an untrusted personal device in an unapproved location.
- Adapting for Hybrid Work: Permissions adjust automatically. An agent working from a secure office network might have broader access than when they log in from a public Wi-Fi network.
- Continuous Monitoring: The system constantly monitors user activity and access patterns. It adapts rules to address changes in behavior or new threats, ensuring policies remain effective.
4. Advanced Multi-Factor Authentication (MFA)
Securing User Credentials
Multi-Factor Authentication (MFA) adds a vital layer of protection beyond just a password. However, traditional MFA methods are becoming increasingly vulnerable. Simple code-based systems, especially those sent via SMS or email, are prime targets for attackers. Phishing attacks targeting MFA credentials are on the rise, with some reports showing they accounted for over 20% of all phishing incidents in late 2023.
Attackers use several common techniques to bypass basic MFA:
- Adversary-in-the-Middle (AiTM) Attacks: Sophisticated phishing sites trick users into entering their credentials and one-time codes, which are then captured and used by the attacker in real time.
- MFA Fatigue: After stealing a password, an attacker bombards the user with push notifications, hoping the user will eventually approve one by mistake just to stop the alerts.
- SIM Swapping: Criminals convince a mobile carrier to transfer a user's phone number to a new SIM card. This allows them to intercept SMS-based verification codes.
These weaknesses show that a modern customer service tool needs a more advanced approach to user security.
The Shift to Passwordless
The future of authentication is passwordless. This approach moves away from vulnerable codes and toward methods that are inherently more secure and user-friendly. By 2026, passwordless options will be a standard expectation for any enterprise-grade software. Research shows that 92% of IT leaders have already adopted or are planning to adopt passwordless authentication.
Passwordless methods are not just a trend; they are a proven strategy. 100% of businesses that adopt FIDO standards report significant improvements in security and user experience.
Leading platforms are embracing phishing-resistant technologies like:
- Biometrics: Using fingerprints or facial recognition on a trusted device.
- FIDO2 Hardware Keys: Physical security keys that provide cryptographic proof of presence.
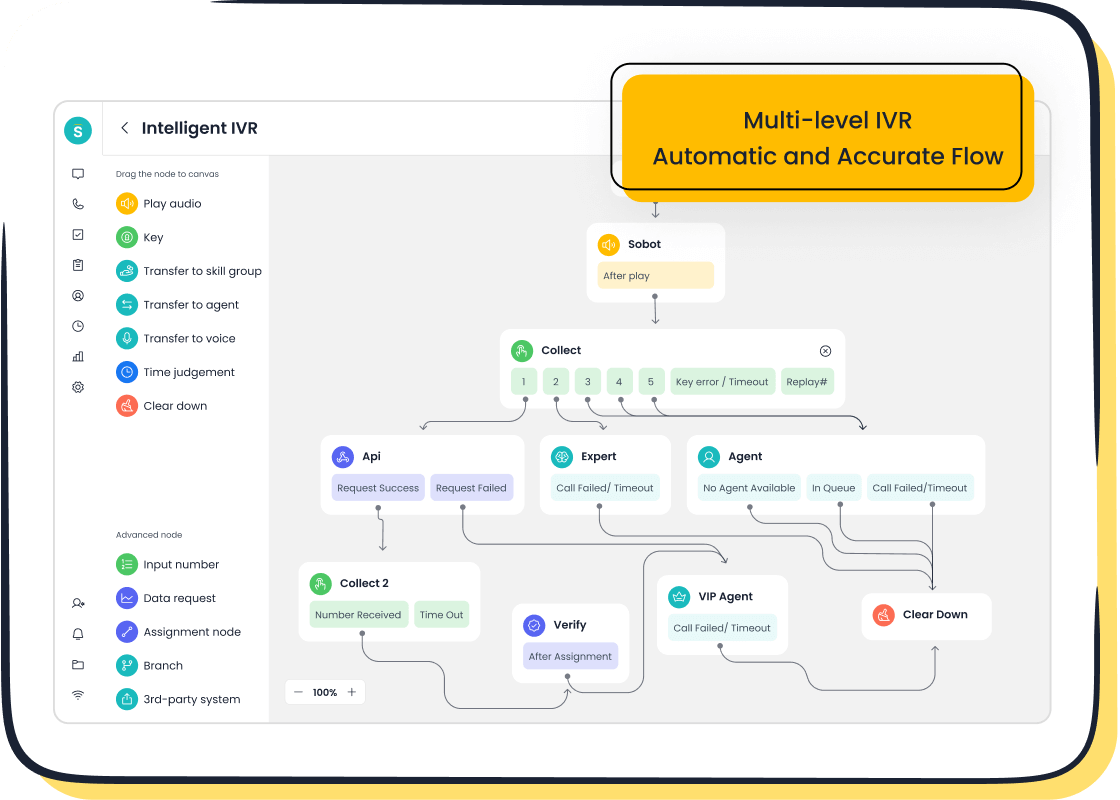
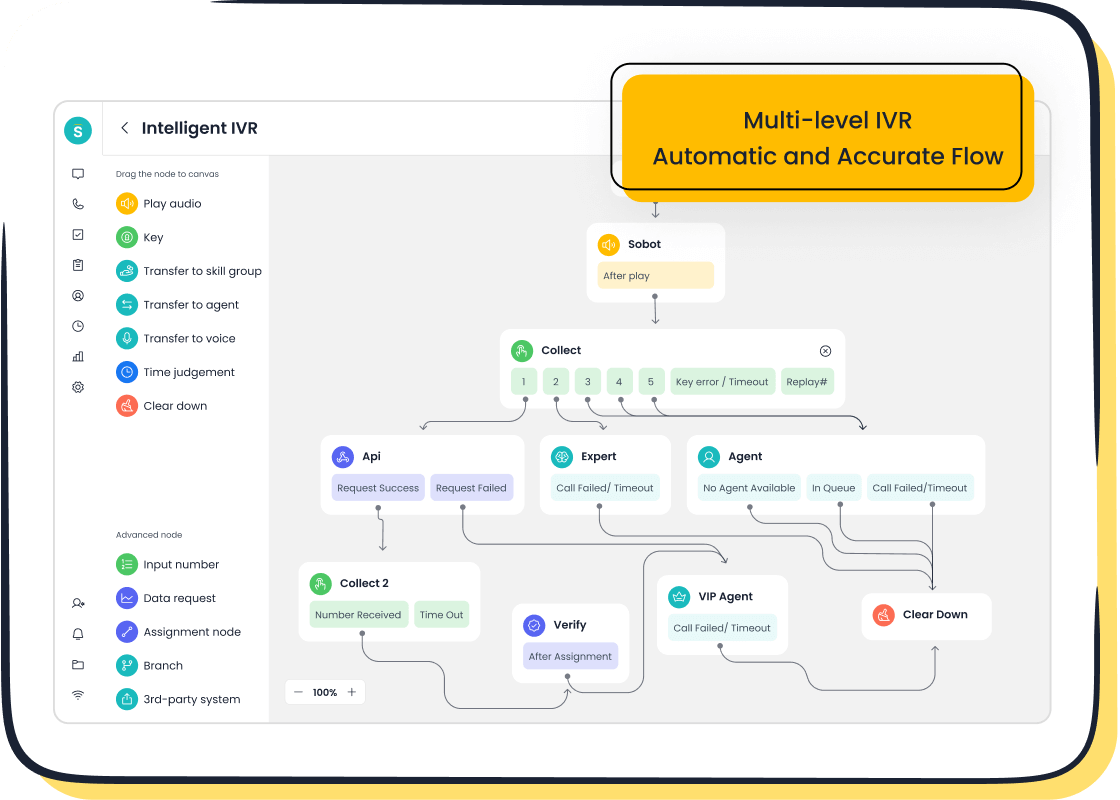
These methods tie authentication to a physical device or a unique biological trait, making them nearly impossible to phish. For platforms like Sobot's Voice/Call Center, which offers mobile app access for agents, robust MFA is essential. It ensures secure agent login from any device, whether in the office or working remotely, protecting sensitive customer data at every access point.
5. Security Information and Event Management (SIEM)
Immutable Audit Trails
Security Information and Event Management (SIEM) systems are the central nervous system for an organization's security monitoring. A modern SIEM platform collects, aggregates, and analyzes log data from across the entire IT environment. For 2026, a critical feature of any SIEM is the immutability of its audit trails. This means once a log is recorded, no one can alter or delete it.
This unchangeable record is essential for forensic investigations following a breach. It provides a trustworthy timeline of events, showing exactly what happened, when it happened, and who was involved. Without immutable logs, attackers could cover their tracks, making an effective response and recovery from an incident nearly impossible. This foundational security capability ensures data integrity for every potential incident. A strong SIEM is the first step in effective security incident management.
AI-Assisted Log Analysis
Traditional SIEM tools required a Security Operations Center (SOC) to manually sift through millions of alerts, an impossible task that led to slow detection and response. Today, AI is transforming Security Information and Event Management. AI-assisted log analysis automates the detection of threats, turning a reactive SIEM into a proactive threat detection and response engine. This is a core function of modern incident response tools and security automation tools.
AI-powered SIEM and SOAR platforms provide the SOC with unparalleled capabilities. These security automation tools rapidly identify threats, filter out false positives, and prioritize genuine alerts for the SOC. This allows the SOC to focus on the most critical threats. The integration of SIEM and SOAR enables an automated response to a detected threat, a key part of the incident response lifecycle. This advanced detection and response is vital for security incident management.
Grammarly's security team provides a powerful example. By using an AI-assisted workflow with their incident response tools, they automated the collection of context for new alerts. This approach reduced investigation time by approximately 90%, improving the SOC team's response and consistency.
This fusion of SIEM, SOAR, and AI creates a powerful defense. The SIEM handles real-time monitoring, the AI provides the intelligence for detection, and the SOAR platform executes the response. This synergy empowers the SOC to manage a higher volume of threats effectively. The right incident management software, powered by SIEM and SOAR, makes this level of detection and response possible. These security automation tools are essential for any modern SOC. The future of incident response tools depends on the tight integration of SIEM and SOAR technologies to counter every threat and incident.
6. Automated Data Redaction and Masking
Protecting Sensitive PII
Customer service interactions are a goldmine for sensitive data. Agents and customers frequently exchange Personally Identifiable Information (PII) through chat, email, and support tickets. This data creates a significant security risk if left unprotected. A single exposed support ticket could contain enough information for identity theft or financial fraud.
A secure customer service tool must prevent this exposure. It needs to identify and protect many types of PII that customers share. Common examples include:
- Personal Details: Full names, home addresses, and email addresses.
- Identification Numbers: Government ID or passport numbers required for verification.
- Financial Data: Credit card numbers, bank account details, and payment histories.
- Login Credentials: Passwords or security keys shared during troubleshooting.
Leaving this information visible in tickets or transcripts creates an unnecessary risk for both the customer and the business.
Real-Time AI-Driven Redaction
Automated data redaction offers a powerful solution. This technology uses AI to automatically find and hide sensitive information in real time. It works across both text conversations and voice call transcriptions. Instead of relying on agents to manually delete data, the system does it instantly and accurately. This proactive approach is essential for maintaining compliance and security.
This feature is especially critical for meeting strict industry regulations like the Payment Card Industry Data Security Standard (PCI DSS). AI-driven redaction directly supports PCI DSS compliance in several key ways:
- It automatically finds and masks credit card numbers, expiration dates, and CVC codes.
- It prevents unencrypted payment data from being sent through messaging channels like email or chat.
- It ensures sensitive numbers are never displayed openly, protecting against both insider threats and accidental leaks.
By automating this process, businesses can effortlessly adhere to complex regulatory standards. Real-time redaction is no longer an optional add-on; it is a core function of any secure customer service tool for 2026.
7. Robust API and Integration Security
Securing Third-Party Vectors
Customer service platforms rarely operate in isolation. They integrate with CRMs, marketing automation tools, and other third-party software. While these connections add power, they also create significant entry points for attackers. A single weak link in this software supply chain can expose your entire system. A common threat emerges from outdated software, where a known vulnerability remains unpatched, giving attackers an easy way in.
These integrations introduce numerous threats. Attackers can exploit a vulnerability in a third-party app to gain unauthorized access or launch a supply chain attack. This can lead to severe consequences, including data leakage, user impersonation, and major business disruptions. Each new connection is a potential threat that requires a planned response. The response to this growing threat landscape must be proactive. A single vulnerability could compromise your entire security posture, making a swift response critical. The initial response to any discovered vulnerability should be immediate containment.
Governance and Vulnerability Scanning
Strong governance provides the necessary framework for a secure response to integration threats. It establishes clear rules and accountability for every API in your ecosystem. Effective governance is not a manual process. It involves embedding automated checks and validations directly into the API lifecycle. This ensures compliance without slowing down development. A key part of this is continuous vulnerability monitoring to find and fix any weakness before it becomes a major threat.
A robust API security policy is the foundation for a strong defense and a timely response. It defines mandatory measures for handling every potential threat. Best practices include:
- Continuous Monitoring: Regularly scan all APIs for any new vulnerability. This includes automated vulnerability scanners and manual penetration tests to identify every possible threat.
- Threat Detection: Use real-time monitoring tools to detect anomalies and trigger an immediate response. This proactive monitoring is essential for a rapid response.
- Access Control: Implement advanced authentication and authorization, such as OAuth 2.1 and short-lived tokens, to protect against a credential-based threat.
- Developer Training: Establish a proactive security culture where developers understand the evolving threat landscape and how to mitigate each vulnerability.
This comprehensive approach to monitoring and governance ensures a fast, effective response to any vulnerability or threat.
8. Geofencing and IP Whitelisting
Geographic Access Restriction
Geofencing creates a virtual perimeter around a real-world geographic area. This technology provides a powerful, automated layer of security for customer service tools. It ensures employees access sensitive systems only from trusted locations, such as a corporate headquarters or an approved home office. This location-based control directly prevents unauthorized access from unsecured networks.
The benefits of this approach are significant. Geofencing adds an invisible, automated layer of protection that requires no user input. It can automatically lock a device or trigger an alert if it leaves a designated safe zone, offering an instant response to potential theft. This capability is crucial for meeting compliance requirements like HIPAA or ISO by limiting where sensitive data can be accessed.
Geofencing allows businesses to define resource availability based on device location. This enforces the principle of least privilege without constant IT oversight, striking a better balance between mobility and security.
Policies for a Hybrid Workforce
Managing access for a global, hybrid workforce presents unique challenges. Traditional IP whitelisting becomes difficult. Remote employees often have dynamic IP addresses that change frequently, creating constant maintenance overhead for IT teams. Manually tracking these changes for a large, mobile team is complex and time-consuming.
Modern customer service platforms must offer smarter policies to address this reality. Effective management requires a structured and automated approach. Key strategies include:
- VPN Integration: Allows remote workers to connect through a company-approved secure channel, presenting a consistent and trusted IP address.
- Node-Based Access Control: Uses cryptographic identities for devices instead of relying on unstable IP addresses for more dynamic and secure control.
- Enhanced Authentication: Triggers additional verification steps, like MFA, when a connection originates from a new or unusual IP address.
A formal change management protocol is essential. This includes regular reviews of IP restriction settings, accurate network documentation, and clear procedures for granting emergency access. This ensures the security requirements for a customer service tool are met without disrupting productivity.
9. Meeting Global Security Requirements for a Customer Service Tool
Proactive Compliance Management
Operating globally means navigating a complex web of data privacy laws. Regulations like GDPR in Europe and CCPA in California are no longer optional considerations. They are strict legal mandates. A modern customer service tool must have built-in features to simplify compliance. Businesses face many challenges in this area.
- Data Mapping: Tracking how and where customer data flows.
- Consent Management: Obtaining clear user consent before collecting data.
- Data Subject Requests: Quickly responding to customer requests to access or delete their information.
Failure to manage these tasks can result in heavy fines and reputational damage. The right platform automates these processes, reducing risk and ensuring consistent compliance. For example, Sobot's AI solution is designed with data privacy and GDPR compliance in mind. It features robust data encryption and continuous encrypted backups. This proactive approach to security and compliance is a core part of the security requirements for a customer service tool. It helps businesses meet their legal obligations effortlessly.
Data Residency and Sovereignty
Data residency refers to the physical location where data is stored. Many countries now have laws requiring their citizens' data to remain within their borders. This creates a significant challenge for global companies. The rules for data storage vary widely by region.
| Region | Data Storage Requirement |
|---|---|
| EU (GDPR) | Allows data transfer to "adequate" countries but often leads to storage within the EU. |
| China (PIPL) | Mandates that data on Chinese citizens must be stored on servers within China. |
| Russia | Requires personal data of Russian citizens to be stored on local servers. |
| U.S. | Has no single federal law, but industry-specific rules (e.g., healthcare) can apply. |
These differing rules make data sovereignty a critical factor. Meeting these security requirements for a customer service tool means choosing a platform that offers flexible data hosting options. A vendor must be able to store your data in a specific geographic region to ensure your compliance. This capability is a non-negotiable part of the security requirements for a customer service tool in 2026, ensuring your operations respect local laws and maintain full compliance.
10. Secure Software Development Lifecycle (SSDLC)
Verifying Vendor Security Posture
A tool's security begins with how it is built. A Secure Software Development Lifecycle (SSDLC) embeds security practices into every stage of the development process. This proactive approach prevents vulnerabilities before they ever reach the final product. A vendor's commitment to SSDLC is a direct indicator of their security posture. A mature SSDLC involves a structured response to risk at every phase. The SOC can leverage security automation tools to improve its response to any incident.
A comprehensive SSDLC includes several key stages:
- Planning: Teams identify security requirements and conduct risk assessments to define controls. This initial response sets the foundation for a secure design.
- Design: Developers create a secure software architecture and identify potential attack vectors. This stage is critical for mitigating any future vulnerability.
- Development: Programmers follow secure coding standards and use security automation tools to remediate any identified vulnerability. The SOC relies on this careful work.
- Testing: The software undergoes automated testing and vulnerability scans to meet security standards. This is a key response to finding a vulnerability.
- Deployment: The team verifies that every vulnerability is fixed and uses ongoing monitoring to ensure a secure production environment. A quick response to any incident is vital.
- Maintenance: The vendor provides regular patches and uses monitoring to address any new vulnerability. The SOC uses security automation tools for a rapid response.
This structured process ensures that security is a continuous focus, not an afterthought. The SOC benefits from security automation tools that provide a better response. The SIEM and SOAR platforms are essential incident response tools.
Transparent Third-Party Audits
Verifying a vendor's SSDLC claims requires objective proof. Transparent third-party audits and certifications provide this validation. These assessments confirm that a vendor not only claims to follow best practices but actually does. They offer customers confidence that the tool is built on a secure foundation. A strong response from the SOC depends on reliable incident response tools.
A vendor’s certifications are more than just badges. They represent a proven commitment to security, verified by an independent authority. This is a critical part of the incident response tools.
For example, a vendor’s commitment to stability and security is often demonstrated through tangible achievements. Platforms like Sobot showcase this through their 99.99% system stability SLA. This level of reliability is the direct result of a rigorous development and maintenance process. Furthermore, becoming an official WhatsApp Business Solution Provider requires passing stringent security vetting. This process examines everything from data handling to infrastructure resilience, confirming a robust SSDLC. This vetting process is a key response to any potential threat. The SOC uses security automation tools to manage any incident. The SIEM and SOAR platforms are key security automation tools. These incident response tools help manage any vulnerability. A quick response to any incident is crucial. The security automation tools provide the best incident response tools.
The digital landscape of 2026 demands a security-first approach to customer service technology. This checklist provides a powerful summary of the essential security requirements for a customer service tool.
Your 2026 Security Checklist:
- E2EE Features
- AI-Powered Threat Detection
- Granular RBAC
- Advanced MFA
- SIEM Integration
- Automated Data Redaction
- Robust API Security
- Geofencing & IP Whitelisting
- Global Compliance Features
- Secure Software Development Lifecycle (SSDLC)
Make these 10 features non-negotiable in your procurement process. Explore solutions like Sobot that build these principles into their core, ensuring your business is secure and future-ready.
FAQ
Why are these 10 security features essential for 2026?
Cyber threats are constantly evolving. Traditional security is no longer enough. These 10 features represent the new minimum standard. They provide proactive defense against modern attacks, protect sensitive customer data, and ensure your business remains secure and compliant in a changing digital landscape.
How do these features help with global compliance like GDPR?
Many features directly support compliance. Data residency options help meet local storage laws. Automated data redaction protects PII as required by GDPR. Granular access controls and immutable audit trails provide the necessary proof of compliance for regulators, reducing legal and financial risks.
What is the most important feature for a hybrid workforce?
Advanced MFA and geofencing are critical for a hybrid workforce. Passwordless MFA secures agent logins from any device or location. Geofencing policies ensure users only access sensitive data from approved areas. Together, they provide strong security without sacrificing flexibility for remote teams.
How can a platform like Sobot meet these security requirements?
Leading platforms integrate these features into their core design. For example, Sobot's AI solution is built with GDPR compliance in mind. Its 99.99% system stability SLA and status as a WhatsApp BSP reflect a commitment to a Secure Software Development Lifecycle (SSDLC).
See Also
Leading 2024 Voice of Customer Platforms: Essential Tools for Business Insights
Discovering the Premier Customer Support Solutions for Businesses in 2024
Optimizing Call Center Performance: Top Speech Analytics Technologies for 2024
Enhancing Customer Engagement: Best Live Chat Support Applications for 2024
Revolutionizing Contact Centers: Top AI-Powered Solutions for Enterprise Operations