What Is Software Security for Customer Service?
Software security for customer service protects your daily tools. This includes platforms like Sobot, ticketing systems, and chatbots. You must ensure the security of customer service software. This practice safeguards customer data and keeps support online. The importance of software security extends beyond IT. It is a business practice for building trust. Understanding various types of software security and software security best practices is key to good cybersecurity. Strong information security, supported by the right software security tools, reinforces your brand's commitment to cybersecurity and information security.
The Importance of Software Security in Customer Service

You might think software security is only for your IT team. This view is a major risk. The importance of software security in customer service is a core business function. It directly impacts your customers, your reputation, and your bottom line. A security failure can undo years of hard work in building customer relationships. Let's explore why strong information security is not just an option, but a necessity.
Protecting Sensitive Customer Data
Your customer service software is a treasure chest of sensitive information. It holds names, email addresses, phone numbers, and support histories. This data is highly valuable to cybercriminals. They can use it for identity theft, phishing scams, or selling it on the dark web. Your primary duty is to protect this information.
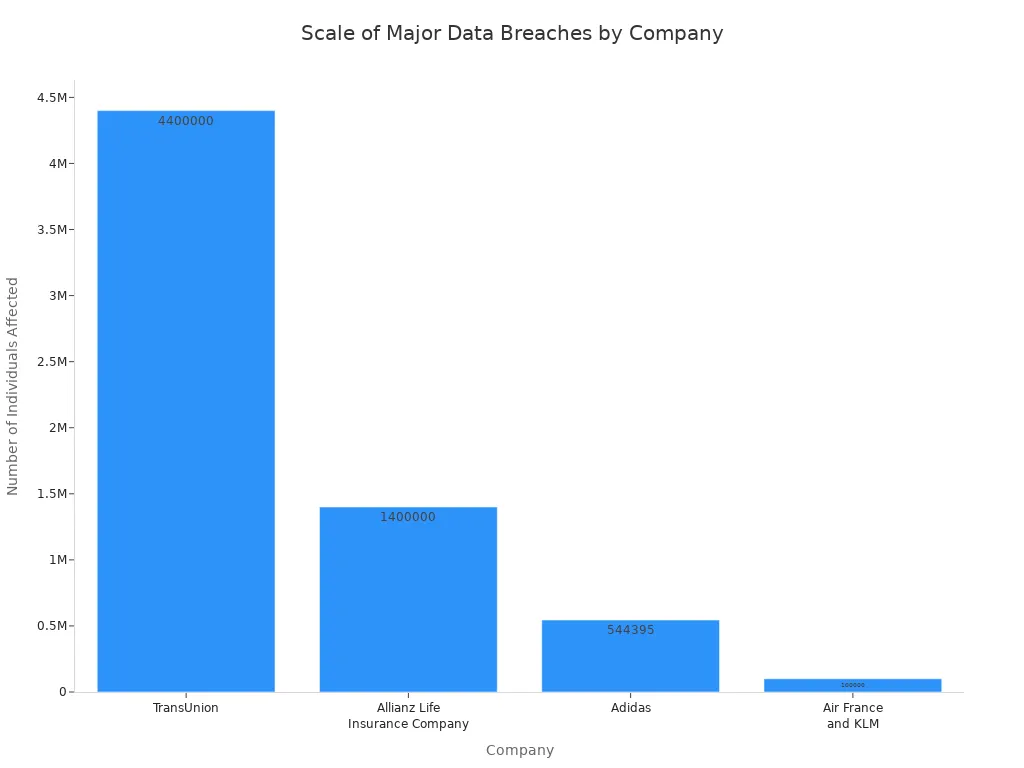
Recent history shows the real-world consequences of failing to do so. Many well-known companies have suffered breaches through their customer service tools, often involving third-party platforms.
| Company | Software Involved | Scale of Breach | Data Exposed |
|---|---|---|---|
| Air France and KLM | Third-party customer support platform | Hundreds of thousands of travelers | Names, email addresses, phone numbers, loyalty program numbers |
| TransUnion | Third-party application for U.S. consumer support operations | Over 4.4 million U.S. individuals | Names, billing addresses, phone numbers, email addresses, dates of birth, Social Security numbers, support tickets |
| Workday | Third-party CRM platform | Undisclosed | Business contact information |
| Adidas | Third-party customer service provider | 544,395 individuals (reported) | Names, email addresses, phone numbers, possibly home addresses and birthdates |
| Allianz Life Insurance | Third-party, cloud-based CRM system | Majority of ~1.4 million U.S. customers | Full names, Social Security numbers, dates of birth, mailing and email addresses, phone numbers, policy numbers |
Attackers often do not need complex hacking skills. Many breaches happen through social engineering. Criminals may impersonate IT support staff. They trick your employees into giving them access. This highlights a critical weakness in the supply chain of customer service. Strong data protection measures are your first line of defense against these threats.
Maintaining Customer Trust and Brand Reputation
A data breach does more than just expose information. It shatters customer trust. When customers give you their data, they expect you to keep it safe. A failure to do so feels like a personal betrayal.
Studies show that nearly two-thirds of consumers lose trust in an organization after a data breach. For many, this damage is permanent. Almost a third of affected customers choose to end their relationship with the company entirely.
This loss of trust has a direct financial impact. A damaged reputation can lead to customer churn and a significant drop in your company's market value. Publicly traded companies often see their stock prices fall immediately after announcing a cybersecurity incident.
- Capital One: Its share price dropped nearly 6% right after a breach disclosure.
- Equifax: The company's share price fell by 60% following its massive 2017 breach.
- General Trend: One study found that companies lose an average of 7.5% of their stock price after a breach.
Regulators also take these incidents seriously. Public companies must now report major cybersecurity events quickly. An incident is "material" if an investor would consider it important. This includes events that harm your reputation or cause customers to leave. This makes strong information security a matter of regulatory compliance and financial stability. The importance of software security has never been greater.
Ensuring Service Availability and Continuity
Effective information security also means keeping your services online. A security incident, like a denial-of-service (DoS) attack, can shut down your customer support channels. When your chat, phone, or ticketing systems go down, your customers are left in the dark. This leads to frustration, missed sales opportunities, and a backlog of support requests that overwhelms your team once service is restored.
The chart below shows the massive scale of individuals affected by just a few recent breaches. An incident of this size causes immense disruption to both customers and company operations.
Industry standards for service availability are measured by uptime. Many top providers promise "Five Nines" or 99.999% uptime in their Service Level Agreements (SLAs). This level of reliability is critical. It means your support tools are available when your customers need them most. You must ensure the security of customer service software not only to prevent data theft but also to guarantee operational continuity. Your customers expect you to be there for them, and high availability is a key part of that promise.
Software Security Best Practices for Your Team

Protecting your customer service operations requires more than just good intentions. You need a clear strategy. Implementing software security best practices is the most effective way to defend your data, your customers, and your brand. These practices turn your team into the first line of defense. They build a culture of security that strengthens your entire organization.
Implementing Secure Access Control
Not everyone on your team needs access to everything. Secure access control is about giving employees access only to the information they need to do their jobs. This is called the principle of least privilege. It is a fundamental concept in information security. Using Role-Based Access Control (RBAC) is a great way to apply this principle. You create roles for different job functions and assign permissions to those roles.
Here is how you can implement RBAC for your team:
- Identify User Groups: Start by categorizing your team members. You might have groups for agents, managers, and administrators.
- Map Roles to Resources: Create a chart that shows which roles can access specific data. For example, a manager might need access to performance reports, while an agent only needs access to their assigned tickets.
- Define Least-Privilege Policies: Begin with a baseline of zero access. Grant permissions one by one as needed for each role.
- Configure Your Policies: Implement these rules in your software. An all-in-one platform like Sobot simplifies this process. You can manage permissions for your live chat, ticketing system, and call center from a single, centralized dashboard.
- Test and Audit Workflows: Before you go live, test the permissions for each role. Make sure agents cannot access manager-level data. Regular audits help you maintain this structure.
- Document Everything: Keep a record of each role and its permissions. This documentation is vital for compliance and future audits.
- Schedule Periodic Audits: Review roles and permissions regularly. This ensures they still align with job responsibilities.
- Avoid Privilege Sprawl: Be careful that employees do not collect unnecessary permissions over time. When someone changes roles, update their access accordingly.
- Automate Deprovisioning: Use automated tools to remove access immediately when an employee leaves your company. This step is critical to prevent unauthorized entry.
Leveraging Data Encryption and Protection
Your customer service software holds a lot of sensitive data. You must protect this data whether it is being stored or being sent across a network. Encryption is the process of converting data into a code to prevent unauthorized access. Understanding different types of software security, like encryption, is key.
There are two main states where you need to encrypt data: at rest and in transit.
| Feature | Encryption at Rest | Encryption in Transit |
|---|---|---|
| Definition | Protects data stored on a physical medium, like a server or hard drive. | Protects data as it moves across a network, like the internet. |
| Purpose | Secures data if a storage device is stolen or a server is breached. | Secures data from being intercepted during communication. |
| Threats Addressed | Physical theft, unauthorized access to files, server breaches. | Man-in-the-middle attacks, eavesdropping, data sniffing. |
| Examples | Encrypting a database of customer tickets or a hard drive with call recordings. | Using HTTPS for your website chat or secure protocols for email. |
Both types of encryption are essential for a complete data protection strategy. Another powerful technique is data masking. This method hides original data with modified content, like symbols or other characters. For example, you can use dynamic data masking to show only the last four digits of a customer's credit card number in a support ticket. This allows your agent to verify the customer without exposing the full number. Techniques like tokenization replace sensitive data with a unique placeholder, adding another strong layer of security.
Protocols to Ensure the Security of Customer Service Software
Strong access control and encryption are pillars of good cybersecurity. You also need clear protocols for your team to follow every day. These rules help ensure the security of customer service software by minimizing human error.
Tip: Strengthen Your Passwords and Use MFA 🛡️ Weak or stolen passwords are a leading cause of data breaches. You must enforce strong password policies. Require your team to create unique passwords and update them regularly. More importantly, you should implement multi-factor authentication (MFA).
MFA adds a crucial layer of security. It requires users to provide two or more verification factors to gain access. Even if a criminal steals a password, they cannot log in without the second factor, such as a code from a mobile app. You must train your team on how to set up and use MFA for all their accounts. This practice is a core component of modern information security and is recommended by frameworks like the NIST Cybersecurity Framework.
Conducting Regular Staff Security Training
Technology alone cannot solve every security problem. Your employees are a critical part of your defense. However, they can also be your biggest vulnerability if they are not trained properly. Regular security training is one of the most effective software security best practices you can adopt.
Studies show the powerful impact of training:
- Organizations can reduce employee-caused security incidents by up to 72% in the first year.
- After just 90 days of training, the rate at which employees click on phishing emails can drop by 40%.
- After a year of consistent training, this rate can fall by as much as 86%.
Training empowers your team to spot and report threats. It covers topics like identifying phishing emails, using strong passwords, and understanding the importance of data privacy. This knowledge helps build a security-conscious culture.
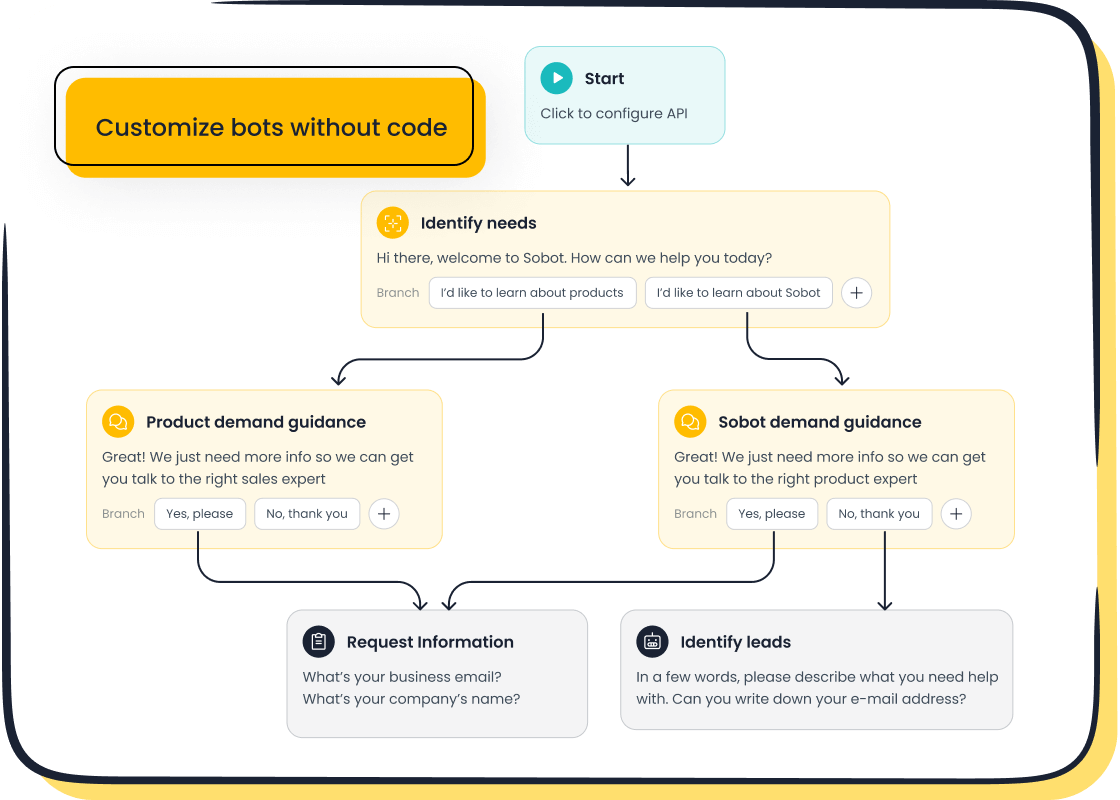
You can also reduce risks by choosing user-friendly tools. For instance, the Sobot Chatbot features a no-code, point-and-click interface. This design allows your customer service team to build and manage automated workflows without writing any code. It enforces consistency and reduces the chance of human error, which helps ensure the security of customer service software. When your tools are intuitive, your team can focus on helping customers instead of navigating complex systems, which is a win for both productivity and cybersecurity.
Evaluating Third-Party Software Security Tools
You cannot build a secure house on a weak foundation. The same is true for your customer service operations. Choosing the right third-party software security tools is a critical decision. You must carefully evaluate any vendor before trusting them with your customer data. This process protects your business and ensures you partner with a company that takes cybersecurity seriously.
Key Questions for Your Platform Vendor
You need to ask direct questions to understand a vendor's security posture. Their answers will reveal their commitment to protecting your information. Here are some essential questions to start with:
- Access Control: How do you manage who can access data? What happens when an employee leaves your company?
- Vulnerability Scans: How often do you test your systems for security weaknesses?
- Data Handling: What are your rules for storing and deleting our data?
- Incident History: Can you share how you handled a past security incident that affected customers?
- Employee Training: What security training do your employees receive?
A transparent vendor will have clear, confident answers to these questions.
Assessing a Vendor's Secure Development Life Cycle
A vendor's development process tells you a lot about their approach to information security. You should look for vendors who use a secure development life cycle (SDLC). This means they build security into their software from the very beginning, not as an afterthought. A strong secure development life cycle includes security checks at every stage, from planning and design to development and maintenance. This proactive approach is much more effective than trying to patch vulnerabilities after a product is released. A mature secure development life cycle shows that a vendor is committed to quality and security.
Verifying Compliance with Data Protection Standards
Promises are not enough. You need proof that a vendor meets industry standards. Ask for compliance certifications for regulations like GDPR or CCPA. You can verify these certificates with the issuing body to confirm they are valid.
Look for benchmarks of trust and reliability. For example, Sobot is an official WhatsApp Business Solution Provider (BSP), a status that requires meeting strict security and data privacy rules. This kind of verification shows a vendor is trusted by major platforms. Furthermore, a provider's commitment to uptime, like Sobot's 99.99% system stability, is a strong indicator of a robust and secure infrastructure. For industries with unique rules, you need specialized software security tools. Sobot's Financial Solution is a great example of a platform designed to meet the strict data protection and compliance needs of the financial sector. This helps you ensure the security of customer service software in a regulated environment.
Software security is a core pillar of modern customer service, not an optional extra. You now understand the importance of software security. Implementing software security best practices and choosing a secure partner like Sobot protects your customer data and brand reputation. As technology evolves with AI-driven threat detection, viewing security as an investment in the customer relationship is key to long-term success. Protect your customers and your business as you Embark on Your Contact Journey.
FAQ
What is software security for customer service?
Software security for customer service protects the tools your team uses daily. It involves safeguarding platforms like your ticketing system and chatbot. This practice keeps sensitive customer data safe and ensures your support operations remain available. It is essential for building and maintaining customer trust.
Why is employee training so important for security?
Your employees are your first line of defense against cyber threats. Regular training teaches them to spot phishing scams and follow security rules.
Remember 💡 A well-trained team significantly reduces the risk of human error. This makes your entire security strategy much stronger.
How do I choose a secure software vendor?
You should ask vendors about their security practices. Verify their compliance with data protection standards like GDPR. Look for signs of reliability, such as official partnerships or high system uptime. A vendor with a secure development life cycle builds security into their products from the start.
What is the difference between encryption at rest and in transit?
Encryption at rest protects data stored on servers or hard drives. Encryption in transit protects data as it moves across a network, like the internet. You need both types. They work together to secure customer information from theft and interception at all times.
See Also
Discover the Top 10 Customer Service Software Solutions for 2024
Essential Tips for Selecting Social Media Customer Service Software Wisely
A Comprehensive Guide to Call Center Quality Assurance Software Excellence
The 10 Best Live Chat Help Software Options for 2024
Unlocking Efficiency: How AI Transforms Customer Service Software Operations