Customer Service Security Requirements 2025
By 2025, your contact center must master three security pillars. You need to secure data everywhere, control agent access, and monitor systems constantly. These are the new customer service security requirements. They are critical for PCI DSS compliance. Failing to meet these DSS standards leads to severe data breaches. After a single data breach, almost 80% of consumers will stop doing business with a company. This guide from Sobot directly answers your most urgent question.
What must my call center do now to be secure and compliant by 2025?
Understanding the Core Customer Service Security Requirements
Meeting 2025 security goals starts with understanding three foundational pillars. These core customer service security requirements protect your operations and build customer trust. You must secure data everywhere, control who accesses it, and watch your systems at all times. This approach is essential for both call center compliance and broader contact center compliance.
Secure Data in Transit and at Rest
Your first duty is to protect sensitive data. Hackers target call centers because they handle valuable information like credit card numbers and personal details. A major vulnerability is the lack of encryption. Unencrypted data, whether moving across your network or stored in a database, is an open target for interception and theft. You must encrypt all sensitive information. This makes the data unreadable to anyone without the correct key, protecting it even if other security measures fail. Strong data security standards are non-negotiable.
Control Agent Access and Behavior
Your agents are your greatest asset and a significant security variable. They need access to sensitive data to do their jobs, but this access creates risk. High employee turnover and social engineering attacks can lead to serious data breaches.
PCI DSS Requirement 7 mandates that you limit access to cardholder data based on a "need-to-know" basis. This means agents should only see the sensitive information absolutely necessary for their role.
Controlling access is a fundamental part of the DSS standards. It helps prevent both accidental exposure and intentional misuse of customer information, directly supporting your compliance efforts.
Maintain Continuous System Monitoring
You cannot protect what you cannot see. Continuous system monitoring gives you real-time visibility into your entire IT environment. It acts as an early warning system, detecting suspicious activities or unauthorized access attempts as they happen. This proactive approach helps you identify threats before they escalate into major incidents. By constantly analyzing system logs and network traffic, you can quickly respond to potential threats, reduce risks, and meet the stringent monitoring standards required by modern customer service security requirements and PCI DSS requirements.
Protecting Data for PCI DSS Compliance

Protecting customer payment information is the cornerstone of the Payment Card Industry Data Security Standard (DSS). To achieve and maintain PCI DSS compliance, you must implement robust technical controls that secure cardholder data at every stage of a transaction. This involves more than just firewalls; it requires a multi-layered strategy that includes encryption, data replacement, and strict controls over recordings. Your goal is to make sensitive data unusable to unauthorized parties, even in the event of a data breach.
Implement End-to-End Encryption (E2EE)
You must encrypt the transmission of cardholder data across all open, public networks. This is a fundamental rule of the Payment Card Industry Data Security Standard. End-to-end encryption (E2EE) is the gold standard for this. E2EE secures communications directly between the two endpoints—for example, the customer and your system. It uses cryptographic keys to lock the data on the sender's device and ensures only the intended recipient can unlock it. No one in the middle, not even your telecom provider, can access the conversation.
For VoIP calls, this involves two key protocols:
- Secure Real-time Transport Protocol (SRTP): This encrypts the actual voice data packets while they are in transit.
- Transport Layer Security (TLS): This encrypts the signaling messages used to set up and manage the call.
A modern call center platform must provide this level of security as a default feature. For example, solutions like Sobot's Voice/Call Center ensure encrypted data transfer and dialing are core functions. This helps you protect cardholder data from the very start of the interaction, a critical step for payment card industry data security.
Utilize Tokenization and Data Masking
The safest way to protect sensitive data is to prevent it from entering your environment in the first place. This is where tokenization and data masking become essential tools for PCI compliance.
Tokenization replaces sensitive card data with a unique, non-sensitive placeholder called a "token." This process ideally happens outside your systems through a validated third-party provider. The token can flow through your applications for reference, but the actual cardholder data never touches your network. This dramatically reduces the scope of your PCI compliance audit and shrinks your cardholder data environments. By integrating your systems with a secure payment gateway that provides tokenization, you can virtually remove your network from the scope of many DSS requirements.
Data Masking protects sensitive data on an agent's screen. It dynamically hides or obscures information, like a credit card number, based on the user's role. The agent sees something like ************1234, allowing them to verify a cardholder without viewing the full number. This helps you enforce "need-to-know" access without disrupting workflows.
Prevent Data Exposure in Recordings
Call recordings are a major liability for PCI compliance. Storing unredacted payment information in call recordings creates significant financial and legal risks. The latest Payment Card Industry Data Security Standard, PCI DSS 4.0, makes it clear that traditional "pause-and-resume" methods for call recordings are no longer enough. You must proactively prevent the capture of sensitive authentication data.
Failing to remove sensitive information from call recordings can lead to severe penalties. Any system that processes voice data containing names, addresses, or card numbers without removing that information is automatically non-compliant. To meet modern call center compliance standards, you must use technology that automatically redacts this information from both audio call recordings and their transcripts. Modern redaction tools use AI and Natural Language Processing (NLP) to:
- Analyze spoken content in real-time.
- Identify sensitive authentication data like PANs and CVV codes.
- Remove the sensitive data from the audio file (with a beep or silence) and the text transcript.
By implementing automated redaction for all call recordings, you protect the cardholder, reduce your liability, and take a critical step toward fulfilling the latest PCI DSS requirements. This ensures your call recordings are secure and compliant.
Implementing Strong Access and Behavior Controls
Securing your data is not just about technology; it's about managing the people who handle it. Your agents are on the front lines, and their actions directly impact your security posture. You must implement strong controls that govern who can access information and what they can do with it. This layer of security is essential for preventing both accidental data leaks and deliberate misuse. By focusing on access controls, authentication, and real-time behavior management, you build a resilient defense for your contact center.
Enforce Strict Role-Based Access Controls (RBAC)
You must limit access to cardholder data based on an agent's specific job duties. This is the principle of least privilege, and it is a core tenet of PCI DSS. Role-Based Access Control (RBAC) is the framework you use to enforce this principle. It ensures agents can only view and interact with the sensitive data absolutely necessary to perform their tasks. This significantly reduces your attack surface and minimizes the potential damage from a compromised account.
Implementing a successful RBAC strategy involves several key steps:
- Define Your Roles: Start by listing every job function in your contact center. Group users based on their access needs, such as 'Tier 1 Support,' 'Sales Agent,' or 'Team Supervisor.'
- Map Permissions: For each role, specify exactly what information and systems they can access. For example, a support agent may need to see a customer's ticket history but not their full payment details.
- Assign Users to Roles: Once roles are defined, assign each user to the appropriate one. Avoid making one-off exceptions, as they create security gaps and are difficult to manage.
- Test and Review: Before a full rollout, test your RBAC model to ensure it works as intended. You must conduct regular audits to remove outdated permissions and verify that roles still align with job functions.
A Unified Approach to Access Control Managing permissions across disconnected systems—like a legacy phone system from Avaya and a separate ticketing tool from Zendesk—is complex and prone to error. A unified platform simplifies this entire process. For example, Sobot's all-in-one contact center solution gives administrators a single dashboard to set granular permissions across every channel, including voice, live chat, chatbot, and ticketing. This ensures consistent security policies and makes auditing far more efficient.
This integrated approach delivers proven results. Financial service leader Opay used Sobot's unified platform to streamline its access controls and customer service operations. The result was a dramatic improvement in both security and efficiency, helping them increase customer satisfaction from 60% to 90% while reducing overall costs. This demonstrates how strong, centralized access controls are foundational to achieving call center compliance and operational excellence.
Mandate Multi-Factor Authentication (MFA)
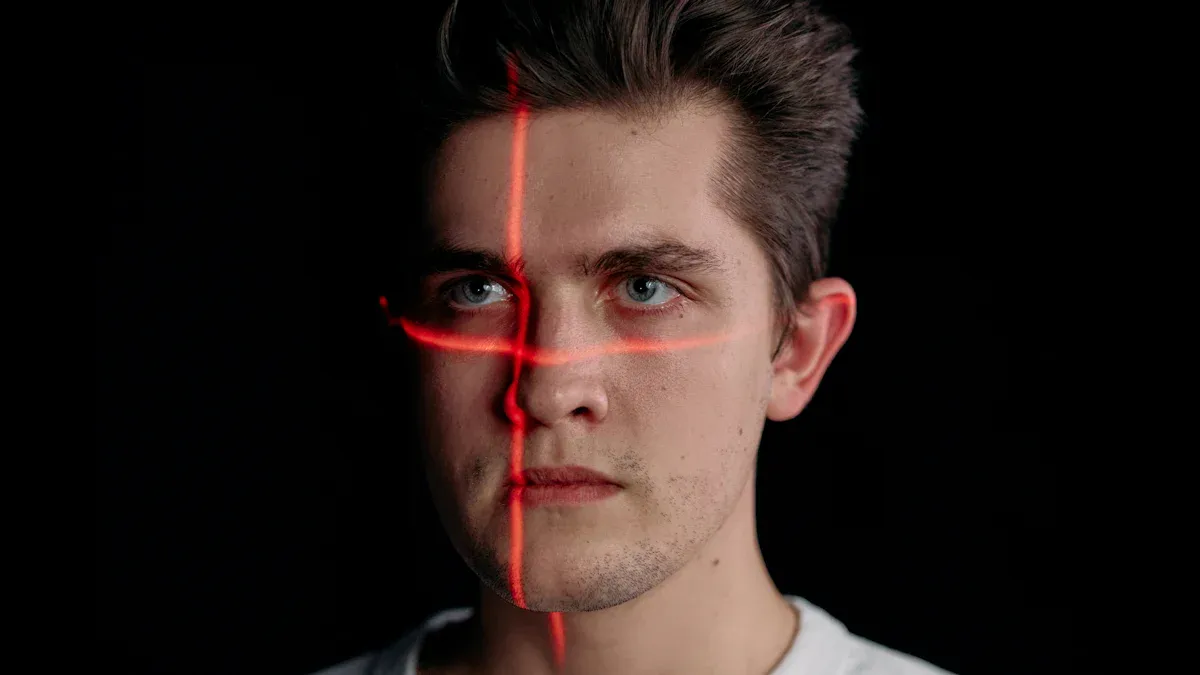
Passwords alone are no longer enough to protect sensitive data. A single compromised password can give an attacker full access to your systems. This is why PCI DSS 4.0 now mandates the use of Multi-Factor Authentication (MFA) for all access into the cardholder data environment. MFA requires a user to provide two or more verification factors to gain access, creating a layered defense that makes it much harder for unauthorized users to log in.
The authentication factors fall into three categories:
- Something you know (e.g., a password or PIN)
- Something you have (e.g., a mobile device with an authenticator app or a hardware token)
- Something you are (e.g., a fingerprint or facial scan)
Under PCI DSS 4.0, your MFA solution must meet strict criteria. It must be configured to:
- Prevent Replay Attacks: An attacker cannot intercept and reuse an old authentication code.
- Block Bypasses: No user, including an administrator, can disable the MFA requirement.
- Use Independent Factors: The system must use at least two factors from different categories listed above.
- Validate All Factors: Access is only granted after all required factors are successfully verified.
Implementing MFA is a non-negotiable step for protecting cardholder data and achieving modern security standards. It ensures that even if a cardholder's or agent's password is stolen, your critical systems remain secure.
Deploy Real-Time Agent Guidance
Even with the best training, agents can make mistakes under pressure. They might accidentally ask a cardholder for sensitive data in a non-secure channel or forget to read a required compliance disclosure. Real-time agent guidance technology acts as a digital co-pilot, providing on-screen support to prevent these errors as they happen. These real-time compliance tools are a game-changer for security.
This technology uses AI to monitor live conversations and provides agents with instant, contextual support. This improves security and compliance by:
- Displaying Compliance Alerts: If a customer starts to read their full credit card number aloud, the system can pop up an alert on the agent's screen, prompting them to interrupt the customer and redirect them to a secure payment IVR.
- Ensuring Script Adherence: The system can provide dynamic checklists to ensure agents follow required security protocols, such as verifying a cardholder's identity before discussing account details.
- Triggering Supervisor Notifications: If a major compliance breach is about to occur, the system can automatically notify a manager, who can intervene immediately.
By deploying real-time guidance, you empower your agents to handle sensitive data correctly on every call. This proactive approach moves beyond simple training and provides an active safety net, helping you maintain compliance, protect customer information, and build a more secure contact center environment.
Your Actionable PCI Compliance Checklist
Achieving compliance is a continuous process, not a one-time fix. You can use this checklist to audit your current practices and build a roadmap for stronger security. This guide will help you prepare for successful pci compliance.
Data Protection Checklist
Your first priority is to protect cardholder data at all times. A strong defense makes data useless to attackers.
- Build a Secure Network: You must install and maintain a firewall to protect cardholder data. Avoid using vendor-supplied defaults for any system passwords or security settings.
- Encrypt All Sensitive Data: You need to encrypt cardholder data both in transit and at rest. Use strong encryption like AES-256.
- Manage Vulnerabilities: Regularly update your anti-virus software and apply security patches promptly. This protects your systems from known threats.
- Test Your Systems: You should regularly test all security systems and processes. This helps you find and fix weaknesses before they can be exploited.
Access Control Checklist
You must control who can access sensitive information. Following the principle of least privilege is a core part of the DSS requirements.
Before any security audits, you must test your access controls. Ensure every user has only the minimum permissions needed for their job. This is a critical step for pci compliance.
- Review Permissions Regularly: You should conduct regular access reviews. Update permissions immediately when an agent's role changes.
- Eliminate Shared Accounts: Every user needs a unique ID. This ensures you can trace all actions back to a specific individual.
- Use Just-in-Time Access: Grant temporary elevated privileges only when necessary. Record all escalations and user activity during that time.
Monitoring and Policy Checklist
Continuous monitoring and clear policies turn your security strategy into daily practice. This is essential for pci dss compliance.
- Create an Incident Response Plan: Your plan must define roles, responsibilities, and communication strategies for a security incident. This is a key DSS requirement.
- Ensure 24/7 Availability: Your incident response personnel must be available around the clock to handle security alerts.
- Train Your Team: You need to provide regular, role-specific training for your incident response team.
- Monitor All Access: Track and monitor all access to network resources and cardholder data. This helps you detect suspicious activity quickly and maintain pci compliance.
Meeting future customer service security requirements is an ongoing commitment. You must continuously invest in advanced security to meet evolving standards. This includes AI-powered monitoring and robust encryption. These efforts protect your data and build customer trust.
Take the First Step Today 🚀 Start by auditing your current data flows and access control policies. Explore how a modern, secure platform like Sobot can help you streamline compliance and master the customer service security requirements for 2025 and beyond.
FAQ
What is the first step to improve my call center's security?
You should start with a security audit. Review your current data protection measures and access control policies. This helps you identify your biggest vulnerabilities. Understanding your weaknesses is the first step toward building a stronger defense and meeting 2025 security requirements.
How does a unified platform like Sobot help with compliance?
A unified platform simplifies security management. It gives you a single place to enforce role-based access controls (RBAC) and monitor agent activity across all channels. This centralized control helps you maintain consistent security policies and makes compliance audits much more efficient.
Why is Multi-Factor Authentication (MFA) so important now?
Passwords are no longer enough to stop attackers. PCI DSS 4.0 now mandates MFA for all access to the cardholder data environment. It adds a critical layer of security. MFA ensures that even if a password is stolen, your systems remain protected.
What is the best way to ensure PCI DSS Compliance in Your Call Center?
You should adopt modern technologies like tokenization and end-to-end encryption. These tools prevent sensitive data from entering your environment. A secure platform like Sobot integrates these features, helping you reduce PCI scope and protect customer data from end to end.
See Also
Essential Principles: A Comprehensive Guide to Call Center QMS Excellence
Discovering the Leading Cloud Contact Center Solutions for 2025's Demands
In-Depth Reviews: Best Cloud Contact Center Services to Consider in 2024
Implementing Effective Quality Management: Best Practices for Call Centers
Ranking the Top 10 Customer Service Software Solutions for 2024